Download FTD and FMC Images and get ready for GNS3 Deployment; Download GNS3 and VMware Images from Cisco Portal; Option 1: Free GNS3 Software - Setup and Installation on your PC or MAC OS; Option 1: Install FMC and FTD templates in GNS3; Option 1: Build Course Lab Topology and Get Started; Option 2: Running FTD and FMC VM Images in Vmware ESXi Environment. .Includes the following version of of the Windows operating system: Windows 7, Windows Server 2008 R2 and Windows 8, 8.1, Windows server 2012 R2, Windows Server 2016 and Windows 10. Also, as Windows 8 RT is a closed system not allowing for 3rd party driver installation our Windows 8 driver will not support this variant of the OS. Connecting the FTDI breakout board to OSEPP™ and Arduino boards: If connecting to a board with 1×6 male pin headers, simple connect the 1×6 female connector to the pin headers. If connecting to a board with pinholes, insert a 1×6 male pin header into the 1×6 female connector, then connect to the board. When connecting the FTDI breakout board, make sure the pin signals match up to the target board's. There is a different driver version for Mac 10.3-10.8 and Mac OS 10.9 and above. Make sure you select the proper one for your OS. When working with most of our FTDI products you are going to be using the FTDI as a 'Virtual Com Port' or VCP. This is important to.
How to Fix FTDI Driver Issue on Mac and macOS
Ongoing macOS FTDI driver issues plague many users connecting the Arduino IDE to boards that use an FTDI chip. Since our boards use an FTDI chip for USB-to-serial communication, we have witnessed some of these issues when working with our boards using Mac and macOS.
The symptoms we have observed generally include the spontaneous loss of the USB serial port connection to the board or loss of the port after disconnecting and then reconnecting the board from the USB programming cable.
Rebooting the system can temporarily restore the port, but the problem eventually comes back. Since we've seen this issue pop up internally and with many customers, we decided to share what solution has been working for us so far.
The exact cause of this problem is not certain, but it seems to be related to Apple's support, or lack thereof, for FTDI drivers in the operating system. Earlier versions of Mac OS X did not support FTDI drivers, so users would have to install third-party FTDI drivers. Somewhere around the release of macOS 10.12 Sierra (and maybe earlier), native support for FTDI drivers was included.
So, if you have followed an upgrade path from an older version of the OS without native FTDI support to a new version that has it, there can be contention between the native and third-party drivers. This potentially leads to the mysterious port disappearance issue.
We have found uninstalling the third-party drivers to be a solution. The instructions below have seemed to work for anyone here at Alorium Technology that was observing the FTDI issues.
Instructions
- To uninstall FTDI drivers you must be logged on to your computer as a root user. Follow Apple's directions if this needs to be enabled on your computer.
- Be careful! By enabling root, you have privileges to change and delete files that are required by your computer.
- Follow steps 4.1 and 4.2 in FTDI Chip's 'FTDI Driver Installation Guide' to uninstall all third-party drivers on your computer.
- Disable root on your computer. Follow Apple's directions below.
- Reboot your system
Want More Info?
Join our mailing list to stay in the loop with the latest news regarding Alorium products and other interesting things we are doing. Your email will not be shared, and we won't pester you very often!
Introduction
This document describes the operation and configuration of the Management Interface on Firepower Threat Defense (FTD).
Prerequisites
Requirements
There are no specific requirements for this document.
Components Used
- FTD running on ASA5508-X hardware appliance
- FTD running on ASA5512-X hardware appliance
- FTD running on FPR9300 hardware appliance
- FMC running 6.1.0 (build 330)
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
Background Information
FTD is a unified software image that can be installed on the following platforms :
- ASA5506-X, ASA5506W-X, ASA5506H-X, ASA5508-X, ASA5516-X
- ASA5512-X, ASA5515-X, ASA5525-X, ASA5545-X, ASA5555-X
- FPR4100, FPR9300
- VMware (ESXi)
- Amazon Web Services (AWS)
- KVM
- ISR router module
The purpose of this document is to demonstrate:
- FTD Management interface architecture on ASA5500-X devices
- FTD Management interface when FDM is used
- FTD Management interface on FP41xx/FP9300 series
- FTD/Firepower Management Center (FMC) integration scenarios
Configure
Management Interface on ASA 5500-X Devices
The Management interface on ASA5506/08/16-X and ASA5512/15/25/45/55-X devices.
This is the image of ASA5506-X:
This is the image of ASA5508-X:
This is the image of ASA5555-X:
When an FTD image is installed on 5506/08/16 the management interface is shown as Management1/1. On 5512/15/25/45/55-X devices this becomes Management0/0. From the FTD Command Line Interface (CLI) this can be verified in the show tech-support output.
Connect to the FTD console and run the command:
ASA5512-X:
Ongoing macOS FTDI driver issues plague many users connecting the Arduino IDE to boards that use an FTDI chip. Since our boards use an FTDI chip for USB-to-serial communication, we have witnessed some of these issues when working with our boards using Mac and macOS.
The symptoms we have observed generally include the spontaneous loss of the USB serial port connection to the board or loss of the port after disconnecting and then reconnecting the board from the USB programming cable.
Rebooting the system can temporarily restore the port, but the problem eventually comes back. Since we've seen this issue pop up internally and with many customers, we decided to share what solution has been working for us so far.
The exact cause of this problem is not certain, but it seems to be related to Apple's support, or lack thereof, for FTDI drivers in the operating system. Earlier versions of Mac OS X did not support FTDI drivers, so users would have to install third-party FTDI drivers. Somewhere around the release of macOS 10.12 Sierra (and maybe earlier), native support for FTDI drivers was included.
So, if you have followed an upgrade path from an older version of the OS without native FTDI support to a new version that has it, there can be contention between the native and third-party drivers. This potentially leads to the mysterious port disappearance issue.
We have found uninstalling the third-party drivers to be a solution. The instructions below have seemed to work for anyone here at Alorium Technology that was observing the FTDI issues.
Instructions
- To uninstall FTDI drivers you must be logged on to your computer as a root user. Follow Apple's directions if this needs to be enabled on your computer.
- Be careful! By enabling root, you have privileges to change and delete files that are required by your computer.
- Follow steps 4.1 and 4.2 in FTDI Chip's 'FTDI Driver Installation Guide' to uninstall all third-party drivers on your computer.
- Disable root on your computer. Follow Apple's directions below.
- Reboot your system
Want More Info?
Join our mailing list to stay in the loop with the latest news regarding Alorium products and other interesting things we are doing. Your email will not be shared, and we won't pester you very often!
Introduction
This document describes the operation and configuration of the Management Interface on Firepower Threat Defense (FTD).
Prerequisites
Requirements
There are no specific requirements for this document.
Components Used
- FTD running on ASA5508-X hardware appliance
- FTD running on ASA5512-X hardware appliance
- FTD running on FPR9300 hardware appliance
- FMC running 6.1.0 (build 330)
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command.
Background Information
FTD is a unified software image that can be installed on the following platforms :
- ASA5506-X, ASA5506W-X, ASA5506H-X, ASA5508-X, ASA5516-X
- ASA5512-X, ASA5515-X, ASA5525-X, ASA5545-X, ASA5555-X
- FPR4100, FPR9300
- VMware (ESXi)
- Amazon Web Services (AWS)
- KVM
- ISR router module
The purpose of this document is to demonstrate:
- FTD Management interface architecture on ASA5500-X devices
- FTD Management interface when FDM is used
- FTD Management interface on FP41xx/FP9300 series
- FTD/Firepower Management Center (FMC) integration scenarios
Configure
Management Interface on ASA 5500-X Devices
The Management interface on ASA5506/08/16-X and ASA5512/15/25/45/55-X devices.
This is the image of ASA5506-X:
This is the image of ASA5508-X:
This is the image of ASA5555-X:
When an FTD image is installed on 5506/08/16 the management interface is shown as Management1/1. On 5512/15/25/45/55-X devices this becomes Management0/0. From the FTD Command Line Interface (CLI) this can be verified in the show tech-support output.
Connect to the FTD console and run the command:
ASA5512-X:
Management Interface Architecture
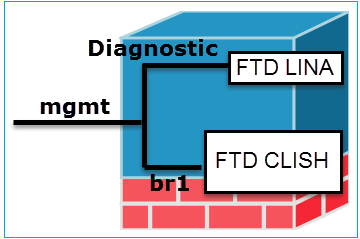
The Management interface is divided into 2 logical interfaces: br1 (management0 on FPR2100/4100/9300 appliances) and diagnostic:
Management - br1/management0 | Management - Diagnostic | |
Purpose |
|
|
Mandatory | Yes, since it is used for FTD/FMC communication (the sftunnel terminates on it) | No and it is not recommended to configure it. The recommendation is to use a data interface instead* (check the note below) |
Configure | This interface is configured during FTD installation (setup). Later you can modify the br1 settings as follows: Step 2. Update the FTD IP on FMC. | The interface can be configured from FMC GUI: Navigate to Devices > Device Management, Select the Edit button and navigate to Interfaces |
Restricting access |
| The access to the diagnostic interface can be controlled by FTD Devices > Platform Settings > Secure Shell and Devices > Platform Settings> HTTP respectively |
Verify | Method 1 - From FTD CLI: Method 2 – From FMC GUI Devices > Device Management > Device > Management | Method 1 - From LINA CLI: Method 2 – From FMC GUI Navigate to Devices > Device Management, select the Edit button and navigate to Interfaces |
* excerpt taken from FTD 6.1 user guide
FTD Logging
- When a user configures FTD logging from Platform Settings, the FTD generates Syslog messages (same as on classic ASA) and can use any Data Interface as a source (including the Diagnostic). An example of a syslog message that is generated in that case:
- On the other hand, when Access Control Policy (ACP) Rule-level logging is enabled the FTD originates these logs through the br1 logical interface as a source. The logs are originated from the FTD br1 subinterface:
Manage FTD with FDM (On-Box Management)
As from 6.1 version, an FTD that is installed on ASA5500-X appliances can be managed either by FMC (off-box management) or by Firepower Device Manager (FDM) (on-box management).
Output from FTD CLISH when the device is managed by FDM:
FDM it uses the br1 logical interface. This can be visualized as:
From FDM UI the management interface is accessible from the Device Dashboard > System Settings > Device Management IP:
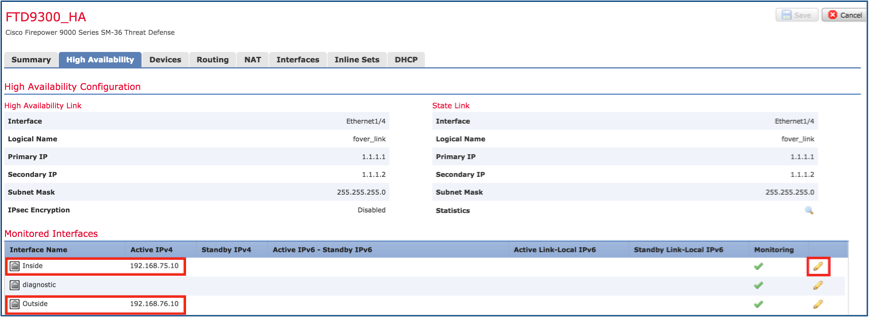
Management Interface on FTD Firepower Hardware Appliances
FTD can be also installed on Firepower 2100, 4100 and 9300 hardware appliances. The Firepower chassis runs its own OS called FXOS while the FTD is installed on a module/blade.
FPR21xx appliance Global game jam 20 mauritius infotainment mac os.
FPR41xx appliance
FPR9300 appliance
On FPR4100/9300 this interface is only for the chassis management and cannot be used/shared with the FTD software that runs inside the FP module. For the FTD module allocate a separate data interface that for the FTD management.
On FPR2100 this interface is shared between the chassis (FXOS) and the FTD logical appliance:
This screenshot is from Firepower Chassis Manager (FCM) UI on FPR4100 where a seperate interface for FTD managment is allocated. In this example Ethernet1/3 is chosen as the FTD management interface: p1
This can be also seen from the Logical Devices tab:p2
On FMC the interface is shown as diagnostic: p3
CLI Verification
Integrate FTD with FMC - Management Scenarios
Given are some of the deployment options that allows to manage FTD that runs on ASA5500-X devices from FMC.
Scenario 1. FTD and FMC on the same subnet.
This is the simplest deployment. As it can be seen in the figure, the FMC is on the same subnet as the FTD br1 interface:
Scenario 2. FTD and FMC on different subnets. Control-plane does not go through the FTD.
In this deployment the FTD must have a route towards the FMC and vice versa. On FTD the next hop is a L3 device (router):